- Coding to an interface
- Service Oriented Architecture
- Automated Testing
- Domain Driven Design
- Custom Data Access Layer
- Layered architecture
Coding Blog
Wednesday, February 24, 2016
Architecture Complexity
Friday, July 31, 2015
IBM Health Center - No JVM Detected on WebSphere 7
Monday, October 27, 2014
Android Studio:Unknown Host Error
Unknown host 'services.gradle.org'. Please ensure the host name is correct. If you are behind an HTTP proxy, please configure the proxy settings either in Android Studio or Gradle. Consult IDE log for more details (Help | Show Log)Solution
File --> Settings --> HTTP Proxy --> Auto-detect proxy settings
Wednesday, December 12, 2012
Exposing WCF Service wsHttpBinding to SoapUI
The message could not be processed. This is most likely because the action ‘[Insert Web Service Action Here]’ is incorrect or because the message contains an invalid or expired security context token or because there is a mismatch between bindings. The security context token would be invalid if the service aborted the channel due to inactivity. To prevent the service from aborting idle sessions prematurely increase the Receive timeout on the service endpoint’s binding.
SoapUI doesn't support security context tokens. Add these lines in Web.config:
Make sure that SoapUI has WS-Addressing set to true.
Thursday, September 20, 2012
C# Builder Pattern
The builder pattern.
using System;
using System.Collections.Generic;
using System.Linq;
using System.Text;
namespace PaymentLibrary
{
public sealed class CardType
{
public string Id { get; private set; }
public string Name { get; private set; }
public string IssueFlag { get; private set; }
public IList<int> Lengths { get; private set; }
public IList<string> Prefixes { get; private set; }
private CardType()
{
}
public sealed class Builder
{
private string id;
private string name;
private string issueFlag;
private IList<int> lengths = new List<int>();
private IList<string> prefixes = new List<string>();
public Builder WithId(string id)
{
this.id = id;
return this;
}
public Builder WithName(string name)
{
this.name = name;
return this;
}
public Builder WithLength(int length)
{
this.lengths.Add(length);
return this;
}
public Builder WithIssueFlag(string issueFlag)
{
this.issueFlag = issueFlag;
return this;
}
public Builder WithPrefix(string prefix)
{
this.prefixes.Add(prefix);
return this;
}
public CardType Build()
{
CardType cardType = new CardType();
cardType.Id = id;
cardType.Name = name;
cardType.IssueFlag = issueFlag;
cardType.Lengths = lengths;
cardType.Prefixes = prefixes;
return cardType;
}
}
}
}
Usage:
CardType cardType = new CardType.Builder()
.WithId("MC")
.WithName("Mastercard")
.WithIssueFlag("N")
.WithPrefix("49")
.WithPrefix("56")
.WithLength(16)
.WithLength(18)
.WithLength(19)
.Build();
Wednesday, July 25, 2012
Brain as the tool of the spirit
The mind as the bridge between pure consciousness and the body in which that consciousness temporarily resides.
Thursday, June 21, 2012
The danger of sharing too much information
Everywhere...
Think twice before you share.
Friday, April 27, 2012
DNS Lookup in Java
import java.net.InetAddress;
import java.net.UnknownHostException;
public class DNSLookup {
public static void main(String... args) {
InetAddress inet = null;
try {
final String host = "eradicus.blogspot.com";
inet = InetAddress.getByName(host);
System.out.println("DNS Lookup: " + host);
System.out.println("IP Adress: " + inet.getHostAddress());
} catch (UnknownHostException e) {
e.printStackTrace();
}
}
}
By using the InetAddress API you will be able to obtain the IP address of the target.
Thursday, April 26, 2012
Reversing a linked list in C++
Link* reverse_list(Link* p)
{
if (p == NULL)
{
return NULL;
}
Link* h = p;
p = p->next;
h->next = NULL;
while(p != NULL)
{
Link* t = p->next;
p->next = h;
h = p;
p = t;
}
return h;
}
Enjoy.
Thursday, March 24, 2011
Fiddler Web Debugging Proxy
Here's a useful tool for debugging web apps specifically running in IE versions 8 and below. This is not just limited to applications running on the browser though, it can listen to any application utilizing HTTP / HTTPS. You do not need to configure your proxy settings to redirect traffic, it just works on the fly.
IE 9 has Developer Tools in it, more info [here] just like FireBug for Firefox and Chrome Developer Tools.
It does not mean that we can not use it though. I would still recommend it for debugging HTTP / HTTPS communication to avoid looking at 3 different tools.
Wednesday, March 23, 2011
Number of Simultaneous Connections in IIS
So I have reached the testing phase of the anti CSRF / CSS / SQL Injection fixes for a classic ASP web application at work. Luckily it didn’t take me long enough to learn the language. My machine will be used for quality assurance purposes. I have encountered an error regarding the number of simultaneous connections made to my local IIS webserver while running OWASP CSRFTester Project.
The fix is simple; just increase the number of simultaneous connections for IIS using the command below:
Assuming your PWD is inetpub\adminscripts
cscript adsutil.vbs set w3svc/MaxConnections 40 iisreset
Sunday, March 20, 2011
Repair Windows 7 System Files
8 out of 10 average PC users have their box’s system files altered by malwares, viruses, etc. We usually reinstall the OS if the antivirus and anti malware software did not perform their job well. Here’s one way to fix the corrupted system files without the need of restarting your Windows 7 box.
1. Run the Command Prompt as Administrator
2. Type the following command
C:\Windows\system32\> sfc /scannow
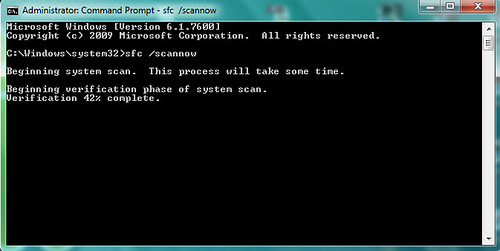
3. After the verification phase, you will receive a message about your system files’ integrity
Windows Resource Protection did not find any integrity violations.
Saturday, March 19, 2011
Android Intent
What is an Android Intent?
- functions like a verb
- something like “open contacts manager”, “search contacts”, “call contact”, and etc.
- I see it something like a description of a method / action to be performed
- used for starting other Activities
You can read more about this here: Android Intent
Monday, March 14, 2011
Android Activity
What is an Android Activity?
- one of the building blocks of an Android application
- used for rendering user interfaces that can respond to events
- a single screen
- can return a value to the previous activity
- pushed into a stack every time a new activity starts
You can read more about this here: Android Activity
Let’s help Japan
Help The Victims of the 8.9 Earthquake in Japan by Spreading Awareness and Aid. Visit http://goo.gl/wjZQz to donate.
